|
Hacked Computer Repair

Based in (Shropshire)
UK Hacking Support
A&A Computer repair is pleased to offer both anti-hacking and ethical hacking services.
We have resolved local - Shropshire computer hacking in Shrewsbury, computer hacking in Telford, computer hacking in Bridgnorth, computer hacking in Broseley, computer hacking in Shifnal and computer hacking in Much Wenlock. In some of the above cases, the hacking attack appears to have originated in Market Drayton, Shropshire.
Sample resolved instances (January to April 2017) include email hacking in Much Wenlock, email hacking in Shrewsbury, email hacking in Telford and network hacking in Bridgnorth.
Computer hackers use a variety of tools to access computers. A common technique is to log onto a computer over the internet, via a nearby remote connection (eg; from a laptop or PC at a nearby location - eg; van in a car park), or by logging onto a network from within the building (eg, by simply plugging a laptop into a network connection.
In many cases, computer hackers are trying to obtain bank account details etc, in other cases the intent is purely malicious.
Manually hacking into a network from an external location is often the result of weak router security. All routers are allocated unique IP (Internet Protocol) Addresses. These addresses can be either floating (they can change) or static (does not change). In the case of a static address, it is possible for a hacker to identify and target a particular IP address and so access the router. If the router has not had the user name and password changed from the default settings, the hacker will often be able access the router and gain access to the network. Computer hackers can then either directly browse data over the network, or install malicious software to search for data such as bank account details, or install software which records keyboard activity (known as key-logging software).
In other cases, people unwittingly allow hackers to access computers by accidentally installing a virus or malware.
This is often the result of clicking on a "dodgy" link whilst online, opening an infected or malicious email, or by allowing access to a hacker as the result of a scam phone call.
Computer Hacking Sample One
Please click above to view
The above is a sample scam email. When victims click on the "view my bill" link, it can install a trojan virus (which can "open the door for malware), or install malware (malicious software) which then searches for personal data and logs keyboard activity.
Computer Hacking Sample Two
Please click above to view
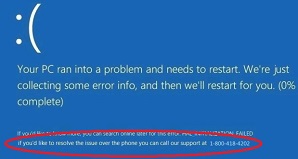
The above shows malware - fake Microsoft Essentials software. This software shows a BSOD (Blue Screen Of Death) screen which prompts the user to phone a hackers phone number. The hacker then pretends to be from Microsoft and they guide the user through a procedure which gives them control of the computer.
Alternatively, they simply request payment of a low amount to resolve the issue and then typically empty the users bank account.
In each case, the risk of infection is greatly reduced by installing quality anti virus software (avoid free options) and high quality anti malware software.
In our experience, Kasperky and Norton are the anti-virus packages of choice whilst Malwarebytes and Hitman Pro are the preferred anti-malware packages (we are very suspicious of Spyhunter "anti-malware" for numerous reasons).